Endpoint Detection and Response (EDR) is one of the most important parts of IT security. It’s responsible for detecting and removing malware and other malicious content in a network. With the myriad of EDR solutions available in the market today, it’s easy to get lost and pick the wrong product. But with F-Secure, users are guaranteed to be protected from malware and other threats.
But what exactly makes F-Secure (now WithSecure) a good EDR solution? F-secure is among the top EDR software products in the market today. It’s an excellent solution because it has proactive threat hunting, excellent data monitoring and management, large network suitability, powerful data analytics, and real-time response and management.
What Makes F-Secure a Good EDR?
With many kinds of businesses starting to rely on computers and networks to run their company, cybercrimes are also becoming worse and more apparent. The cost of damages caused by cyberattacks globally is predicted to increase up to $6 Trillion and it’s only expected to rise every year.
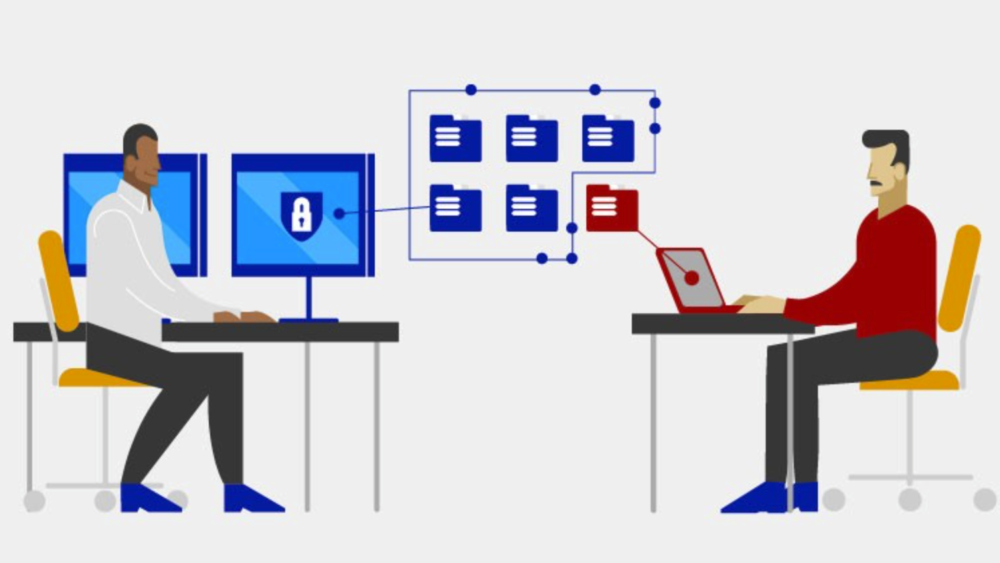
Since firewalls and other traditional network protection programs are becoming weaker against new types of attacks, it’s better to invest in a more secure solution like EDR software. This kind of program focuses on threat hunting, investigation, and mitigation on both the networks and the endpoints.
One of the best EDR software products recommended in the market today is the F-Secure Rapid Detection & Response. Here are some of its features that make it a worthwhile investment to protect the organization against cyberattacks:
Proactive Threat Hunting
With cyber threats becoming more aggressive, it’s not enough to just have reactive management to get rid of malicious behavior and other security issues. EDR solutions actively look for potential threats before they attack the endpoint or the network. The software automatically solves the problem using different remedial actions.
Hackers have started creating threats and malware that easily get through the usual antiviruses. EDR solutions like F-Secure detect even the malware with polymorphic codes that evolve on their own. The software decides on the best corrective action to get rid of the threat immediately.
Excellent Data Monitoring and Management
F-Secure is designed to collect and monitor the data on all the endpoints in the network. It compiles all the needed data for monitoring potential cyber threats to the network. All the collected data are stored in a database on the endpoints.
All the important data are analyzed to determine the main cause of the security issues. This kind of information is useful for detecting other malware moving forward. It also allows F-Secure to create stronger and more suitable solutions, as well as response and management strategies to prevent the attack or minimize the damages.
Suitable for Larger Networks
Larger business networks become more prone to cyberattacks because there are more vulnerable endpoints to monitor. Traditional antiviruses aren’t enough to protect these kinds of massive networks.
But F-Secure EDR solutions are created to cater to such networks. The software quickly collects and monitors the data on all the endpoints in the network to study them. This feature of F-Secure Rapid Detection & Response makes it a must-have for strengthening the network’s cybersecurity. It also makes it easier for the IT experts in the company to observe the systems daily.
Powerful Data Analytics
F-Secure also comes with powerful analytical tools to identify the threats even in its early stages. This allows the program and the team to deal with the malware effectively before it causes further damage to the network. The program also comes with a feature that minimizes the false positives in the network to minimize alert fatigue.
The EDR software’s powerful data analytics also help place the detection into context. It presents how the threat possibly attacks and impacts the affected hosts. This makes it easier for the IT security team to create a suitable solution that minimizes damages.
Real-Time Response and Management
F-Secure is excellent when it comes to collecting and monitoring relevant data about malware footprints and other kinds of potential threats to the endpoints and the entire network. All important information necessary to create suitable responses is collected in real-time. It’s also updated frequently to provide the appropriate information that helps IT teams keep the network secure.
Certain cyber threats are immediately managed by the EDR software as they develop in the network. The program designs incident management responses early on to get rid of the threat before it causes further damage. The forensic data collected during the process also helps cut down investigation and preparation time needed by the IT security team.
Bonus: “Elevate to F-Secure” Feature
Sometimes, the network encounters threats that aren’t easily fixed by the EDR tool. Complex detections like these require a deep analysis by a cybersecurity expert. With F-Secure’s “Elevate to F-Secure” feature, the IT team has direct contact with F-Secure consultants.
These experts have easy access to the incident data. Upon examining the threat, they provide instructions to the IT team to help them solve the case.
Other Endpoint Detection and Response Tools
With the plethora of EDR tools available in the market today, finding a suitable program for a business might be a difficult task. There are tons of features and factors to consider. A program with lots of features might sound tempting, but it’s not wise to spend more money on software that has a hundred features when you only need ten.
Here are other EDR tools in the market that also scored high on different tests and reviews:
Microsoft
Microsoft has stepped up its game when it comes to cybersecurity. The strongest point of Microsoft Defender is that it’s already integrated into the Windows source code. The program provides standard features to make the endpoint and the network secure.
However, the program lacks the analyst workflow that most EDR tools have. It also requires users to pay for other additional features like VPN and rogue device discovery. Microsoft defender is already a good tool by itself, but it’s better to invest in a more robust security system if the business heavily depends on having an extremely secure network.
Bitdefender
Bitdefender is one of the best picks for small to midsize businesses. It has basic features that startup companies might need. Some of the more advanced tools come at additional costs, but Bitdefender already has good automation features. This software is a good pick for starters, but it’s also worth investing in if the company decides that the advanced tools and features are necessary for different operations.
Protect Yourself from Cyber Attacks with Abacus
Cyberattacks cost businesses hundreds of dollars, which is why investing in an excellent security system is a must. Here at Abacus, our team of support personnel and engineers is ready to provide comprehensive solutions to keep your network and endpoints secure.
Learn more about our extensive set of services from fixing projects to fixed-budget all-in-one support by visiting our website now. Call us at (856) 505 – 6860 to get started on the best IT solutions that fit your needs.


Comments are closed.